The access control policy is the undisputed foundation of any serious information security programme. Despite this consensus, a significant number of organisations in the tech industry operate with policies that are cumbersome, outdated, or simply ineffective. These policies often struggle to keep pace with dynamic cloud environments, remote workforces, and complex regulatory landscapes.
This results in a security paradox: a policy exists, yet breaches and compliance failures remain a persistent risk. For security and engineering leaders, this operational friction is a major strategic hurdle. It demonstrates a clear disconnect between the theoretical goal of security and the real world demands of the business.
This case study reveals the proven four stage framework Overt Software Solutions uses to address this exact challenge. We move beyond simple rule sets to design policies that are not only compliant and robust, but also seamlessly integrate with modern, high velocity software environments. Our approach ensures that your security posture is a business enabler not a bottleneck.
Understanding the Policy Failure Points
The path to an effective access control policy begins by accurately analysing why current policies so often fail to deliver. The root cause is rarely malicious intent; it is usually a systemic overreliance on outdated models and a failure to align policy with user workflow.
The Limits of Traditional RBAC
Role Based Access Control RBAC has been the industry standard for decades and remains a foundational concept. It allocates permissions based on a users job role or function within the organisation. For small or static environments, RBAC offers simplicity and clear governance.
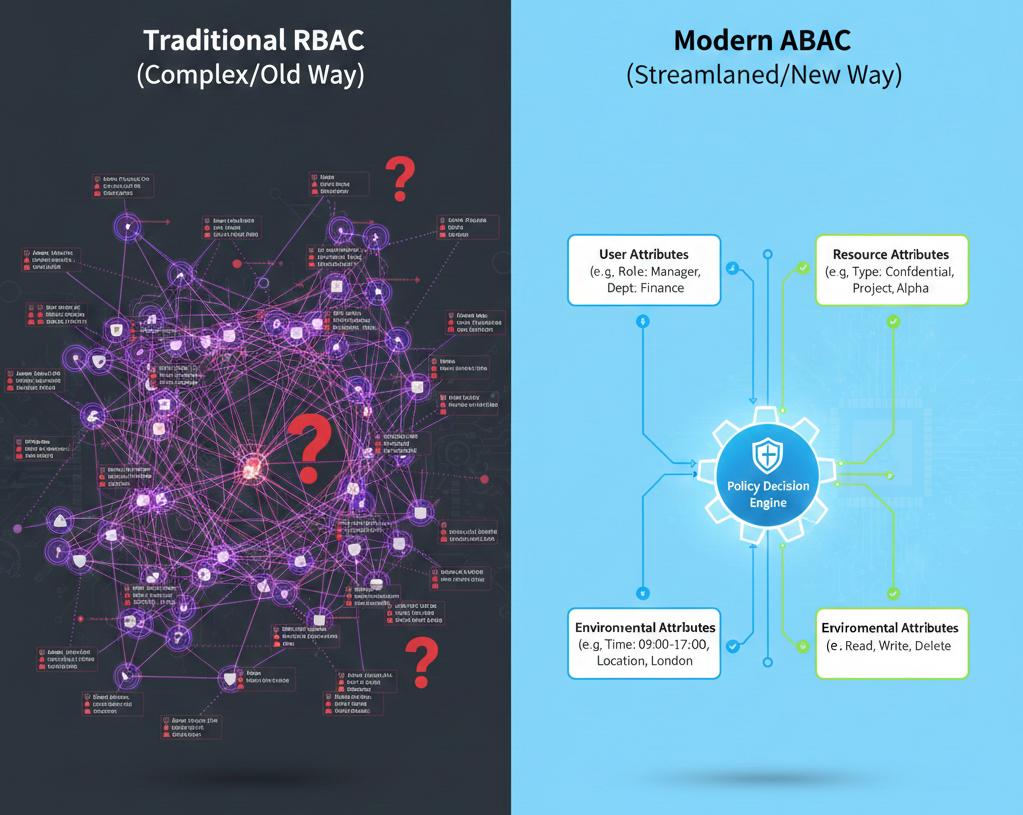
However, in large scale or dynamic software environments, RBAC quickly descends into complexity. As job roles become more granular and projects cross functional, security teams are forced to create a sprawling network of specific roles. This is known as role explosion. A security administrator can spend all their time managing these roles rather than focusing on strategic defence, leading to:
- Excessive Privilege: Users often receive permissions they do not actually need to avoid the complexity of granular role assignment, violating the principle of least privilege.
- Maintenance Overhead: Updating permissions for one user can require modifying permissions across dozens of interconnected roles, making policy changes slow and error prone.
Compliance Over Function
Another major failure point is designing a policy with compliance alone in mind. While meeting standards like ISO 27001 or GDPR is non negotiable, an effective policy must treat compliance as an outcome of good design, not the sole objective.
Policies designed purely for checklist ticking often overlook real world user workflows. If a policy is too restrictive and makes essential tasks difficult or impossible, users will find workarounds. This introduces shadow IT and unmonitored processes that undermine the entire security framework. A policy must balance strict security controls with usability to ensure high adoption and compliance enforcement.
The Human Element
Ultimately, access control policies are enforced by technology but designed for people. Policies that are vague, poorly documented, or inconsistent create user confusion and anxiety. If employees cannot easily understand what they are authorised to access and why, it leads to:
- Support Costs: Increased security help desk tickets as users struggle with permissions.
- Operational Delay: Time lost waiting for manual approval or resolution of unclear access rights.
- Security Fatigue: Users stop paying attention to security protocols because the system is deemed frustrating and unreliable.
A successful policy requires clear communication, consistent enforcement, and a structure that is logical to the person using it.
The Overt Approach: A Four Stage Policy Design Framework
An effective access control policy is not a static document; it is a continuously refined operational framework. The Overt approach systematic and iterative. It shifts the focus from managing user roles to managing the context of the access attempt. This is how we design a policy that is dynamic, scalable, and genuinely secure.

A. Stage 1: Discovery and Risk Analyse
The process begins not with code but with a comprehensive understanding of the operational landscape. Many policy efforts fail because they focus on who a user is rather than what they need to do.
This stage requires detailed data mapping and risk quantification:
- Asset Inventory and Classification: Every resource must be identified and classified by sensitivity (eg public, internal, confidential, or restricted). This defines the protection required.
- Workflow Mapping: We conduct in depth stakeholder interviews across development, operations, and business teams. This uncovers the precise permissions users require to complete their core tasks without friction. This analysis identifies where current policies are causing bottlenecks or workarounds.
- Regulatory Benchmarking: All applicable external standards (eg HIPAA, SOC 2, ISO 27001) are mapped directly to the access requirements. This ensures that compliance is built into the policy structure from day one.
B. Stage 2: Policy Modelling and Selection
With the requirements clearly defined, we determine the most appropriate technological model. This is the crucial point where we often move beyond the limitations of basic RBAC.
For modern software solutions that handle large volumes of diverse data, we recommend the shift to Attribute Based Access Control (ABAC) or a robust hybrid model.
ABAC grants access based on a combination of attributes, making the policy exponentially more granular and flexible:
- User Attributes: Job title, department, security clearance, project status.
- Resource Attributes: Data classification, file owner, creation date, location.
- Environmental Attributes: Time of day, geographical location, device used.
Instead of defining fixed roles, the policy engine evaluates complex statements like Allow access if the user is a Manager in London and the resource is marked Internal and the time is between 9am and 5pm. This flexibility inherently implements the principle of least privilege and reduces the risk of role explosion.
C. Stage 3: Policy Translation and Documentation
Once the model is selected, the high level security objectives must be translated into enforceable, unambiguous rulesets. The policy translation phase is where rigour prevents confusion.
- Creating Rulesets: Policies are translated into policy definition languages (PDLs) that the underlying identity and access management IAM systems can process. This ensures consistency and prevents misinterpretation during implementation.
- User Centred Documentation: We create tiered documentation. Technical teams receive precise ruleset specifications, but end users receive clear, concise summaries written in plain language. This manages user expectations and reduces the perception of security as an obstacle. The documentation should be easily searchable and accessible.
- Policy Versioning: Establish a formal system for version control and change logging. This maintains an audit trail and ensures that all stakeholders are aware of active and historical policy states.
D. Stage 4: Testing and Auditing Strategy
A policy is only truly effective if its enforcement is flawless and continuous. This stage focuses on proactive verification and accountability.
- Policy Simulation and Testing: Before deployment, the rulesets are rigorously tested against real world scenarios using policy simulation tools. This identifies conflicts or gaps in coverage before they can be exploited. This proactive testing is critical for mitigating risk.
- Automated Auditing: Establish regular, automated audits that verify the policy implementation is correct and that no user has gained unauthorised access. This provides continuous assurance of the security posture.
- Review Cycle: Policies must evolve. We implement a mandatory, systematic review cycle (eg quarterly or half yearly) to check if the policy still aligns with current business operations and the latest threat landscape. This ensures the policy remains relevant and functional over time.
Case Study Insight: The Impact of a Well Designed Policy
To demonstrate the real world value of this four stage framework, consider the experience of a global financial technology client. Like many rapidly growing organisations, they relied heavily on a legacy RBAC system. This had led to classic role explosion; their security team was managing over 350 highly specific roles across their internal and external facing applications. The complexity was staggering, making compliance audits slow and operational changes risky.
Before the Change
- Risk: An internal audit revealed that 30 percent of employees possessed permissions that exceeded the principle of least privilege due to broad role assignments.
- Friction: New employee onboarding and offboarding took up to two full days of security administrator time just for permission provisioning.
After Implementing the Overt Framework
We applied the four stage framework, moving their critical systems to a hybrid ABAC model. This meant permissions were defined by context (eg the users department and the current project) rather than fixed roles.
The measurable results were significant:
- Security Posture Improvement: The total number of required access rules was consolidated by 65 percent, leading to a massive reduction in complexity and exposure.
- Administrative Efficiency: The time spent managing user permissions was reduced by 70 percent. New users are automatically provisioned based on dynamic attributes, freeing security professionals for strategic work.
- Audit Confidence: Compliance with critical regulations is now demonstrable through clear, attribute based logic that is easily auditable.
The result was a robust security framework that actually accelerated business operations by making access control automated, predictable, and fully scalable.
Key Takeaways
Designing an access control policy that actually works requires abandoning the hope that simple, static models can solve modern security challenges. The key to long term success is adopting a structured, people centred methodology that prioritises the principle of least privilege while leveraging the flexibility of models like ABAC.
A policy that is both secure and functional is a powerful asset. It reduces administrative burden, improves compliance confidence, and enables development teams to move faster without compromising security integrity. By following a proven framework for analyse, design, translation, and continuous auditing, organisations can transform their access control policy into a true foundation of their security posture.
Is your organisations security being slowed down by an outdated, overly complex access control policy? Overt Software Solutions specialises in providing expert led policy design and implementation services.
Contact us today to discuss how our team can revolutionise your security framework, ensuring your access control is robust, compliant, and perfectly aligned with your business objectives.
