Introduction: What is Adware?
Adware is malicious software that pops out or displays advertisements on your computer, most often within a web browser. Today’s engineers refer to adware as a “Modern-PUP” (potentially unwanted programs). PUPs are unwanted pieces of software that try to trick users into installing them. They often disguise themselves as legitimate software or piggyback on another program to fool users into letting them install.
Brief history of Adware
In 1990, the term” Adware” was first used by security researcher and computer scientist Yisrael Radai. In 1995, the term became officially used by all computer engineers. Previously, ad-supported software was considered to be spyware. They were considered “legitimate” because legal businesses with actual offices and payrolls created them. Soon, though, security professionals started differentiating between adware and spyware as less harmful forms of PUPs.
Adware affiliates / Round tripping on legitimate businesses. often spread their adware without being checked by adware vendors. This allowed them to increase adware through peer-to-peer sites, botnets, instant messaging infections, and browser hijacks.
BuddiBonzi is an excellent example of an adware affiliate. BuddiBonzi is a freeware virtual assistant that manages downloads, sings songs, shares jokes and facts, and carries out other functions on command from its user. BuddiBonzi owner makes deals with retail companies to advertise the retail company’s products digitally, drive advertisements to every user’s computer to impose as a virtual assistant, and have more users download the freeware and install it on their PC. When most people download and install BuddiBonzi for interactives, their browser gets hijacked and receives multiple ads and popups.
As adware companies became more aggressive, some started closing down affiliates engaging in bad behaviour. These moves were a common response after the peak years of adware. As governing authorities started to issue large fines for these violations, the biggest adware companies just picked up their code and left. This pattern of activity was common during the peak years of adware (2005-2008). More recently, browsers have been cracking down on adware with ad blockers, causing websites to lose revenue from legitimate adverts (ads).
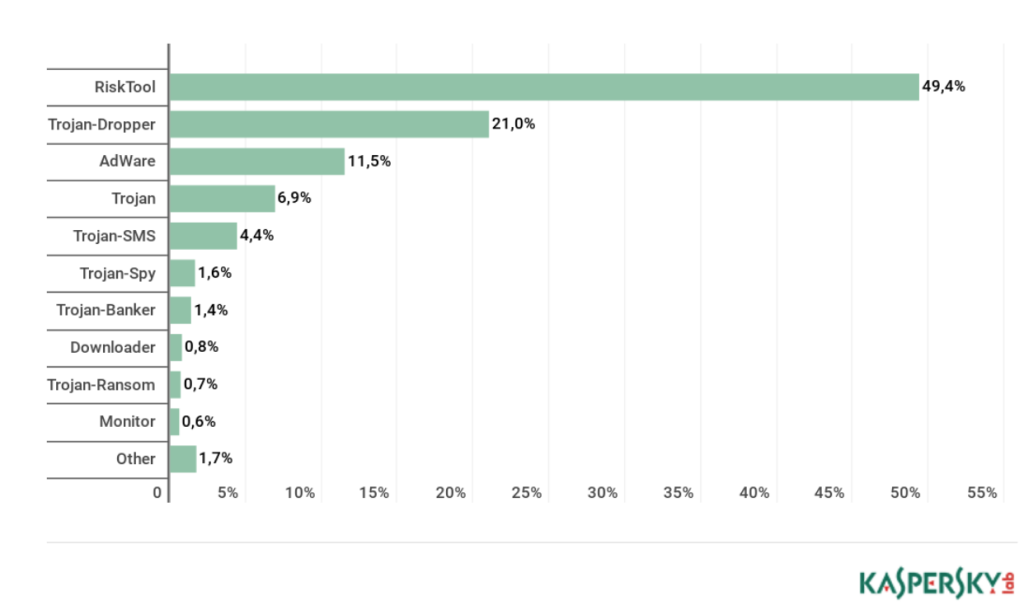
Although adware still exists today, it is usually viewed as a form of PUP (potentially unwanted program). Adware presents a threat level below malware but still ranks high among consumer detections. Based on a research conducted by the Kaspersky Lab, Within the second half of 2018, Adware ranked behind Trojan (E.g. Dropper / Emotet) as the number one consumer detection.
One reason might be the volume of adware increasing on mobile devices, likely because most adware is making its way into mobile apps. However, adware makers today are consolidating power by using techniques more aggressively than simply hijacking users’ browsers and hiding within Trojans or bundling with ad fraud components.
Adware in mobile devices
There are two ways that adware can come to your phone: through your browser and via downloaded apps.
Via downloaded apps
Downloaded apps can carry unwanted ads that display on your phone in different forms, such as full screen ads inside and outside of the infected app, to notifications on the lock screen. Typically, third-party app stores install this kind of adware app.
To avoid these risks, download apps only from trusted sources, such as Google Play or App Store.
Via browsers
Infection by browser refers to a known exploit that can lead to ad pop-ups on an affected device. Advertisers know about this exploit and how to use it to get their ads seen.
The best way to prevent this from happening is to use a different browser, disable JavaScript, or install a browser with ad blocking. Another remedy to pop-ups is to back out of them using Android’s back key. Or you can clear your history and cache, which will also stop the ads from coming back.
Adware: Browser hijackers
Most adware strategies qualify as browser hijackers. They specialise in changing your Internet browser settings without your knowledge or consent. Typically, hijackers change the home page and default search settings. You might be happily surfing along when suddenly you see an ad pummeling you. Since ads appear in a pop-up or pop-under form, they seem to originate from the site you’re visiting.
Thus, there are many different types of adware programs, which can change your start page or search engine, or even mess with the shortcuts on your computer that open your browsers. Here are some of the well known browswer hijackers that used to have notorious reputation;
Fireball
Fireball is a browser hijacker created by the Rafotech digital marketing agency. It comes bundled with other software made by this company (Mustang Browser and Deal Wifi) and is installed along with these programs without your knowledge. Once it infects your computer, it changes your homepage to Trotux, a fake search engine, and inserts ads into any web page you visit. It also prevents you from modifying your browser settings.
Although there’s still no proof that this adware example does anything besides hijacking your browser and flooding it with ads experts worry that Rafotech could decided to launch a cyber attack using this software.Due to the number of infected systems worldwide, the consequences, if they chose to launch an attack, would be devastating.
Appearch
Another common adware program is Appearch. Appearch will hijack your browser and make surfing the Web a nightmare; Appearch will redirect you to Appearch.info whenever you try to visit a website, and it will insert ads into the websites you visit, so surfing the Web becomes frustratingly difficult. Even if you manage to open a webpage, Appearch will change random blocks of text into links, so when you select text on a page, an ad for software you don’t want will appear.
When you visit a website with limited access, Appearch may show you a pop-up message asking you to subscribe to notifications. As soon as you subscribe, Appearch will start showing you pop-up ads even while your browser is closed.
Gator
Now inactive. Gator was an adware program that pioneered the concept of behavioral marketing to much controversy. The controversial software was bundled with popular free programs. This meant that if visitors clicked on an ad, all profits went directly to Gator instead of content creators.
Nevertheless, Gator was most notorious for its policy of recording people’s complete browsing histories and even parts of their credit card numbers. They would then use this information to provide them with better targeted ads. Although such practices are widespread now, it was unheard of in the 2000s.
In 2003, Gator’s developer changed its name to Claria Corporation and continued to release adware until 2006; two years later, the company was shut down.
DeskAd
DeskAd is a common adware program that deceives users by displaying deceptive ads, redirecting their traffic to suspicious websites, and showing pop-up ads. As opposed to other adware programs, DeskAd starts off very discreetly only to gradually take full control of your browser.
DeskAd will often be sent to you as an email attachment. It changes the settings on your computer, so that it can run on startup. DeskAd also makes many copies of itself, which can slow down both your memory and processor and cause your computer to crash. If it is used on a network of computers, it could cause widespread problems for everyone using those computers.
Adware Symptoms
If you think your computer may be infected with adware, look for one or more of these following signs:
- Your browser is not running as smoothly as it used to and might be crashing often.
- Some websites are starting to include ads and banners, which they never did before.
- You’re unable to change your browser homepage format back to its original settings.
- You are noticing your browser is displaying new toolbars, plugins, or extensions.
- You are constantly redirected to different pages whenever you try to visit a website.
- Your computer starts installing apps without your permission and you don’t know how to stop it.
- When you click anywhere on the page, a pop-up ad appears.
How did your device/computer get infected with Adware?
Adware can get onto your system in two ways.
- Number one: you download a popular program that you know and trust or a program that offers to install extra features. Adware is often included in free software. It is possible to get adware from freeware and shareware because the program’s author signed up with an adware vendor. The author gets paid by the ad company, and users get a free program.
- The second method that causes your device to get infected with adware is visiting a website. Maybe it is a trusted site, but it can also be deceptive. Either way, the website might be infected with adware which often takes advantage of the user’s browser’s vulnerability to deliver a drive-through download.
After it burrows in, the adware displays more advertisements in your browser, collects your personal information, and directs you to various malicious websites.
How to protect yourself from Adware?
When you know how adware works and take the necessary precautions to protect yourself from it, you can enjoy an adware-free online life. Here are some essential safeguards you can take to get better protection online.
- Ensuring you follow computer and software cyber safety best practices is essential.
- Always think twice before downloading new software and stop the download process if you suspect something suspicious, like permission to load adware.
- Read the terms of the agreement carefully before you install anything.
- Never download illegal files and never open emails from unknown sources.
- Download a reputable antivirus and firewall program for your mobile device and computer.
- Keep your application and software up to date and perform scans frequently.
As you know, we can be the weakest link regarding security breaches. To help ensure your network is safe, it’s essential to follow best practices and educate yourself on staying secure. Regular training and teaching of best practices are highly recommended to upgrade your human firewall.

