The Foundation of Zero Trust The Principle of Least Privilege
In the security landscape of 2026 traditional network firewalls have become secondary to the true perimeter identity. As organisations continue to adopt cloud native architectures and remote working models the way access is managed determines the resilience of the entire business. At the heart of this shift is the Principle of Least Privilege or PoLP.
PoLP is not merely a security checkbox. It is a proactive risk reduction strategy that ensures every user process and device has only the minimum permissions necessary to complete a specific task. By strictly limiting access an organisation creates a digital circuit breaker. If a single account is compromised the damage is contained within a small area rather than allowing an attacker to move freely across the entire network. This limitation of the blast radius is essential for maintaining operational integrity during a security event.
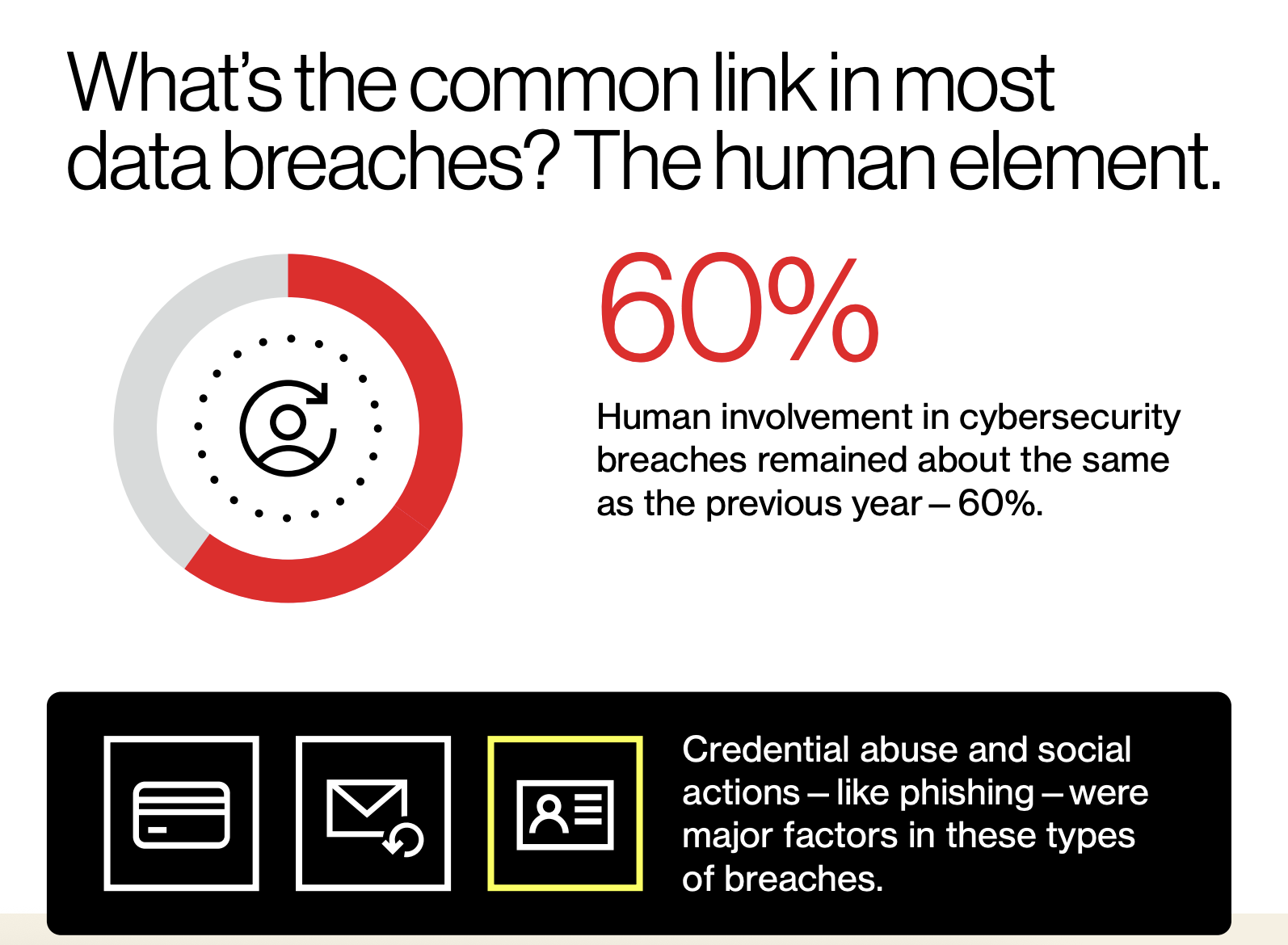
The necessity of this approach is backed by significant data. Research from the 2025 Verizon Data Breach Investigations Report indicates that over 60 percent of breaches involve the human element including stolen credentials and social engineering. Implementing least privilege is the most effective way to ensure that a stolen password does not grant an attacker the keys to the kingdom.
The Architecture of Access Effective Role Design
To implement least privilege effectively an organisation must move away from ad hoc permissions toward structured role design. A common pitfall for many technology firms is the accumulation of Identity Debt often caused by Role Sprawl. This occurs when companies create hundreds of hyper specific roles based on internal job titles rather than actual system functions.
The gold standard for modern governance is functional abstraction. A useful benchmark is the 80 20 rule of role design. If 80 percent of users in a specific role utilise 80 percent of the permissions assigned to that role then the abstraction level is likely correct. This balance reduces the complexity for IT administrators and simplifies the audit process for compliance teams.
Effective roles should be built around enduring business functions such as Invoice Processing or System Configuration rather than volatile organisational charts. By designing roles this way permissions remain stable even when employees join leave or change titles. Furthermore, a robust design must incorporate Separation of Duties or SoD. This ensures that no single role has enough power to both initiate and approve a high risk action which is a critical requirement for financial and data security regulations.
Beyond Static RBAC The Future of Access Governance
As we look toward 2026 static Role Based Access Control or RBAC is no longer sufficient on its own. The industry is moving toward more dynamic and context aware models to combat sophisticated identity threats. This evolution focuses on several key technological shifts:
- Zero Standing Privileges: In this model users do not have permanent administrative rights. This removes the risk of long lived high privilege accounts that are often the primary target for attackers.
- Just In Time JIT Access: This mechanism ensures that elevated permissions are granted only for a specific authorised window of time and for a specific task. Once the work is finished the access is automatically revoked.
- AI Driven Role Mining: Many organisations are now using artificial intelligence to analyse actual user behaviour. These tools identify permissions that are never used and suggest slimmer more accurate role definitions that reflect reality.
- Contextual Authentication: The future of access governance is a hybrid of roles and attributes. While a role provides the basic structure attributes provide the vital context such as whether a user is logging in from a managed device or a recognised geographic location.
This level of granular control is what defines a mature security posture in the modern era. It ensures that security is not a static barrier but a fluid system that adapts to the risk level of every individual request.
Key Takeaways and Strategic Alignment
Building a culture of secure access is an ongoing journey that requires both the right philosophy and the right technology. Manual processes and spreadsheets are the enemies of effective governance. To stay ahead of threats organisations must automate the lifecycle of identity ensuring that access is provisioned and deprovisioned in real time as the workforce evolves.
As 2026 begins Overt Software Solutions is here to support reliable systems and dependable support. Helping organisations stay protected prepared and confident as technology continues to evolve.
Our expertise in identity providers and automated lifecycle management allows us to help you implement the complex logic flows required for modern least privilege and role design.
Get in touch to see how our advanced security platform can support a stronger security foundation for your organisation.
