Massive regulatory fines, reputational damage, and loss of customer trust are the tangible consequences of failing to protect customer and employee data under the General Data Protection Regulation GDPR. For many organisations, the largest single point of failure in their compliance strategy lies in identity management.
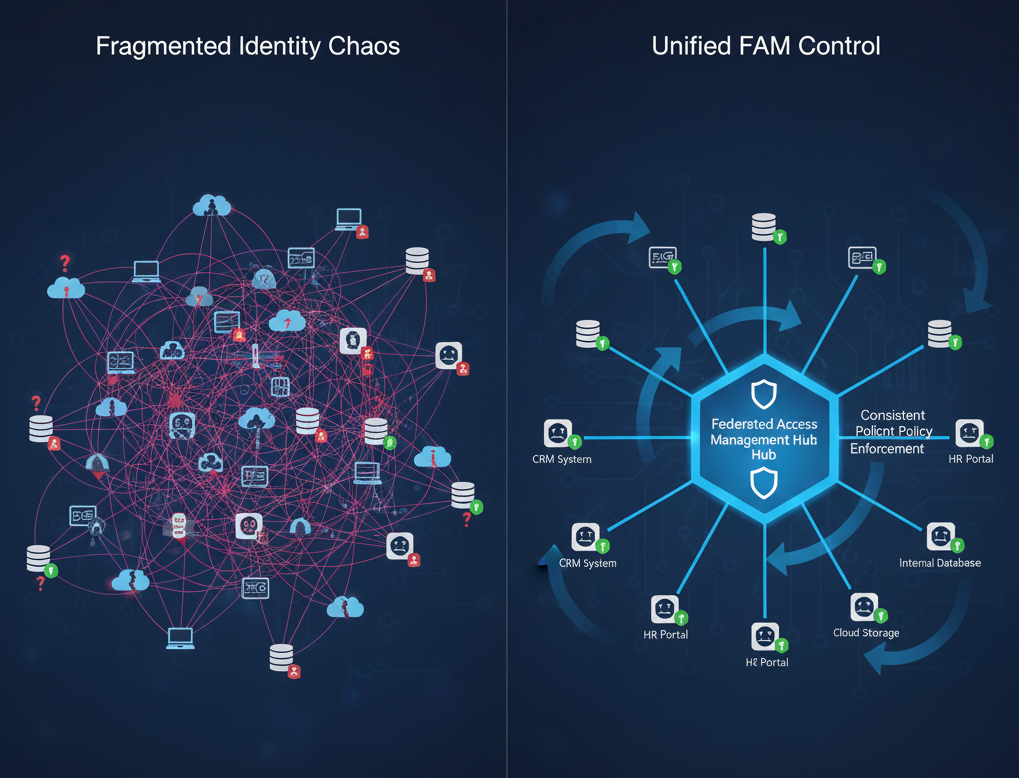
Fragmented identity systems are the silent enablers of GDPR non compliance. When identity data is scattered across dozens of individual applications, cloud services, and legacy systems, it is impossible to guarantee that security controls are consistent or that access can be revoked instantly.
This complexity creates unacceptable risk. This post will show that achieving audit ready GDPR compliance is no longer a matter of manual checks and balances; it requires a unified technical solution. The essential blueprint is Federated Access Management FAM. FAM provides the centralised control and single source of truth mandatory for meeting the toughest regulatory standards.
The Compliance Challenge: GDPR Articles and Identity
While the GDPR contains many complex requirements, several key articles pose a direct and persistent threat to organisations with fragmented identity infrastructure. Failure to meet the demands of these articles can lead directly to penalties.
Violation 1: Article 5 Data Minimisation and Integrity
Article 5 requires personal data to be processed with integrity, confidentiality, and kept only as long as necessary. Fragmented identity systems routinely violate this by perpetuating access bloat.
If a user changes roles or projects, they may retain old permissions across a dozen siloed applications simply because the IT team lacks a single tool to manage that lifecycle. This over provisioning of access is a direct violation of the principle of data minimisation, unnecessarily expanding the attack surface and increasing the scope of any potential breach.
Violation 2: Article 17 Right to Erasure
The Right to Erasure is one of the most operationally challenging requirements of the GDPR. It mandates that when a data subject (e.g. an employee or customer) requests their data be deleted, the organisation must act swiftly to erase it across all systems where it is processed.
When an employee leaves the company, their identity must be immediately de provisioned. If their account permissions are scattered across dozens of systems, manually revoking access is slow, error prone, and almost impossible to verify instantly. This leaves a critical window where the former employees access remains active in some applications, representing a clear and immediate breach of Article 17.
Violation 3: Article 32 Security of Processing
Article 32 requires organisations to implement appropriate technical and organisational measures to ensure a level of security appropriate to the risk. The presence of multiple, disconnected identity stores makes consistent security impossible.
One application might enforce Multi Factor Authentication MFA while another uses simple, weak passwords. This inconsistency provides an attacker with the weakest entry point into the entire ecosystem, compromising the entire chain of trust. Fragmented systems cannot enforce a unified security baseline, leaving the organisation short of the Article 32 mandate.
The Federated Access Solution
The solution to compliance chaos is centralisation. Federated Access Management FAM is the mechanism that allows an organisation to establish a Single Source of Truth SSOT for every users identity and access profile. This single source is typically the organisations core directory, such as Active Directory.
Core Principle: Single Source of Truth
FAM operates by acting as the trusted broker between the user, their identity provider (the SSOT), and all service providers (the applications). Rather than creating individual accounts with disparate passwords and permission lists on every single application, FAM uses standardised protocols like SAML or OAuth.
When a user attempts to access any application, the application redirects the request back to the central FAM platform. The FAM platform verifies the users identity, checks their current role and status in the SSOT, and then releases only the minimum necessary information required to grant access.
This simple shift from fragmented, decentralised verification to a unified, centralised security gateway has profound implications for GDPR compliance.
Compliance Critical Features of FAM
FAM is not just about convenience through Single Sign On SSO; it is a critical instrument of identity governance, designed to enforce the specific requirements of the GDPR.
Centralised Provisioning and De-provisioning
The challenge of the Right to Erasure (Article 17) is instantly met by FAM automation.

When an employee leaves the company or their identity status changes in the central Active Directory, the FAM platform instantly initiates a de provisioning workflow. This workflow automatically revokes their access across every single application that is federated, regardless of whether it is a cloud service or an on premises database. This automatic, auditable, and immediate revocation guarantees compliance with the undue delay clause of Article 17, eliminating the window of vulnerability created by manual processes.
Zero Trust and Least Privilege
FAM is an enforcement mechanism for the principles of Zero Trust and Least Privilege, thereby satisfying the Data Minimisation mandate of Article 5.
The system ensures that a user is only granted the minimum access rights necessary to perform their current job. Crucially, when an application requests access attributes for a user, the FAM policy engine only releases the required data (e.g., job title and department) and nothing more. The applications never hold the full, sensitive identity profile, reducing the data footprint and scope of any potential breach.
Strong Authentication Standardisation
To address the Security of Processing requirement of Article 32, FAM mandates and unifies the use of Multi Factor Authentication MFA across the entire application portfolio.
If the central FAM platform requires a token or biometric verification, every application federated through it inherits that strong security requirement. This eliminates the compliance threat posed by legacy applications with weak password policies, establishing a consistent, high security baseline across the entire organisation.

Strategic Implementation and Auditability
Implementing Federated Access Management is a major undertaking, but the strategic benefits for compliance and security are clear. For the solution to deliver true GDPR assurance, it must excel in two areas: auditability and integration flexibility.
Comprehensive Audit Trails
Proving compliance to an auditor is just as important as being compliant. FAM platforms must provide comprehensive, detailed audit trails that log every single access event and policy decision.
This includes logging:
- The users identity and access attempt.
- The exact attributes released to the application.
- The specific policy rule that was enforced (eg MFA was required).
- The automated de provisioning action taken.
This rigorous logging provides an unassailable record. Instead of relying on manual attestations, the organisation can present verifiable, consistent evidence that demonstrates adherence to Article 5 and Article 32 policies across the entire application ecosystem.
Integration Flexibility
A true enterprise solution must bridge the gap between legacy on premises systems and modern cloud applications. Organisations often have mission critical applications that predate modern federation protocols.
A robust FAM platform must be capable of integrating these disparate applications into the centralised security architecture. This unified approach ensures that compliance and security standards are applied consistently, preventing any application from becoming a weak link in the identity chain. Choosing a platform that offers custom integration capabilities is essential for ensuring every part of your identity landscape is brought under the centralised control required for GDPR compliance.
Key Takeaways
The complexity of the GDPR requires a definitive technical response. Attempting to manage the demands of the Right to Erasure and Data Minimisation using fragmented, manual identity tools is a strategy guaranteed to fail.
Federated Access Management FAM is the necessary technical pivot. By establishing a single source of truth and automating the enforcement of identity policies and lifecycle events, FAM transforms an organisations security posture from one of inherent risk into one of audit ready reliance. It moves identity governance from a costly administrative burden to an automated, central pillar of compliance.
Is your organisations identity infrastructure introducing unacceptable GDPR risk?
Overt Software Solutions are experts in designing and deploying custom Federated Access Management solutions that provide the centralised control and rigorous audit trails required for enterprise compliance. Contact us today to secure your identity lifecycle and ensure your business is fully protected against regulatory exposure.
