Shibboleth Integration for Your Moodle Platform
Numerous organisations and companies implement Shibboleth to ensure secure access for their employees to various applications. It is specifically designed to safeguard network resources and applications against unauthorised access. In summary, Shibboleth is a web authentication and authorisation system, operates within the HTTP layer. Similar mechanisms apply to Apache and IIS. I.e.;
- In this setup, the Shibboleth Service Provider (SP) acts as the client, with web applications running within the SP.
- The SP receives variables from the Attribute Authority, a remote source that is part of an Identity Provider (IdP) within a Federation.
- Multiple IdPs can exist within a Federation.
These variables represent attributes and are made available in the httpd process as variables. To integrate them into web applications, the variables need to be connected appropriately. Integrating the Moodle and Shibboleth authentication modules is widely acknowledged as a highly prevalent practice.
Shibboleth Authentication System Streamline
The Shibboleth protocol facilitates the interaction between the IdP and SP, which is built on top of the Security Assertion Markup Language (SAML).
SAML operates on the HTTP layer, providing a secure framework for exchanging authentication and authorisation information.
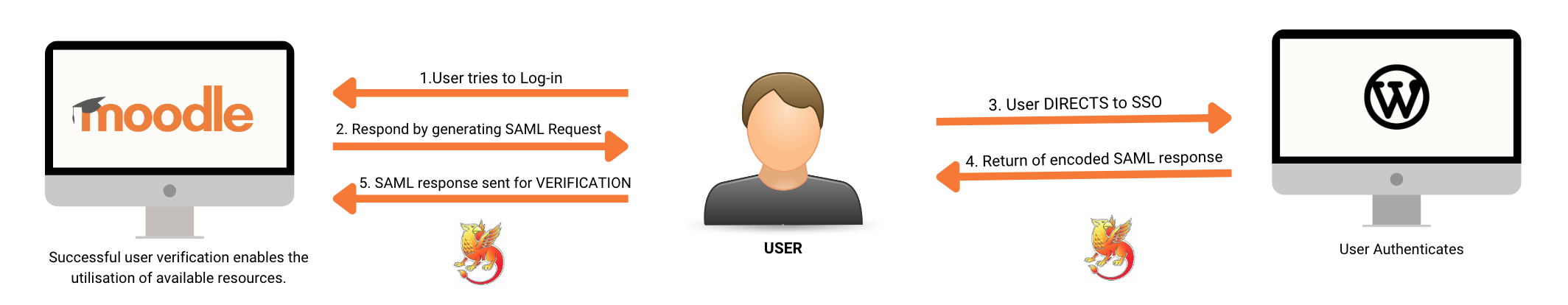
Shibboleth enables trust relationships between the IdP and SP. This involves the exchange of X509 certificates and key pairs. The IdP can control which attributes are provided to the SPs and within the SP.
The communication between the IdP and SP occurs over HTTPS, adding a layer of security. While the initial setup may require some effort, it is simple, particularly for those familiar with setting up services like Apache and MySQL.
Why Choose Shibboleth?
Shibboleth offers a significant advantage by enabling Single Sign-On (SSO) using the user's "home IdP" username and password. The Identity Provider (IdP) retrieves user account details from an LDAP directory during this process. Shibboleth can be viewed as an enhanced version of LDAP, providing robust functionality. Leveraging Shibboleth eliminates the need for the Service Provider (SP) to have direct access to the LDAP, enhancing security and instilling confidence in LDAP administrators and security personnel.
Here are a few benefits of using Shibboleth and Moodle together.
- Allow you to seamlessly login to Moodle using shibboleth and allowing one set of credentials to authenticate the user (this can be using the Active Directory credentials for example).
- Most institutions tend to have Moodle as one of the first pages for their users so enabling shibboleth on Moodle allows users to seamlessly access the Moodle as soon as the browser loads and then once authenticated to seamlessly (without logging in again) to move on to other resources .
- Using one set of credentials increases security as users will not need to remember multiple passwords (which generally leads to users writing down the passwords in clear text).
- Shibboleth enables fine-grained access control to Moodle resources, allowing administrators to define and enforce access policies based on user attributes or roles.
- Shibboleth and Moodle integration can efficiently handle large user bases, making it suitable for organisations or institutions with a significant number of users.
We have very competitive prices for shibboleth enabling your Moodle so if you would like more information please contact us on success@overtsoftware.com or alternatively call Overt Software directly on 01905 955037.
Overt Software offer a wide range of services involving shibboleth so we can protect any internal or external resources that you have.

